“You will never learn, if you don’t build-break-fix on your own” – I had always been sceptical of this thought when one of my mentors told me this a long time back. But slowly, during the course of my IT journey, I realized he wasn’t correct… he was more than correct! Whenever I tried building and had hands-on of my own…..I not only learned, but I also started enjoying and became more passionate to dig deep and learn more.
And thus, “Build – Break – Fix – Learn – Document” has become a core value of my IT journey & IT experience, from a long time. Below are some of the pointers (and NOT a full-fledged comprehensive practice plan!) that really helped triggering and strengthening some of my IT-support/IT security-related foundations. Sharing below some of the quick pointers that may be helpful, and hoping to motivate your IT journey.
Try creating your own “Home Security Lab” and practice on below three scenarios which may give very interesting insights.
CAUTION on Ethical Hacking practices: Ethical hacking must only be performed on systems you own or have explicit written permission to test. Unauthorized access, scanning, or exploitation of networks is illegal and can lead to severe legal consequences. Always follow applicable laws, organizational policies, and responsible disclosure practices when identifying and reporting vulnerabilities.
I . Scanning with Nmap

Scanning with nmap also known as Pen Testing.
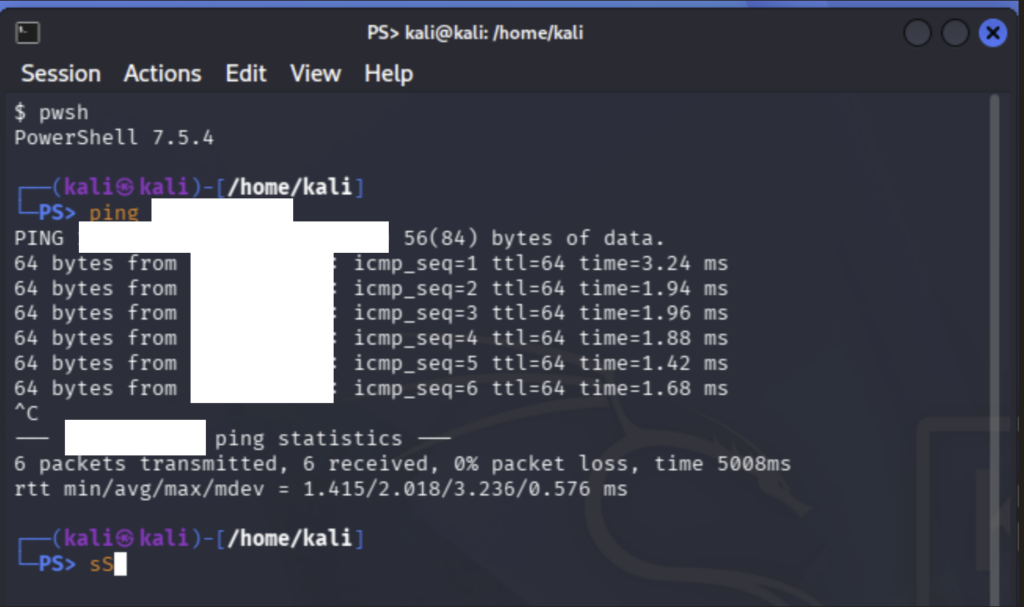
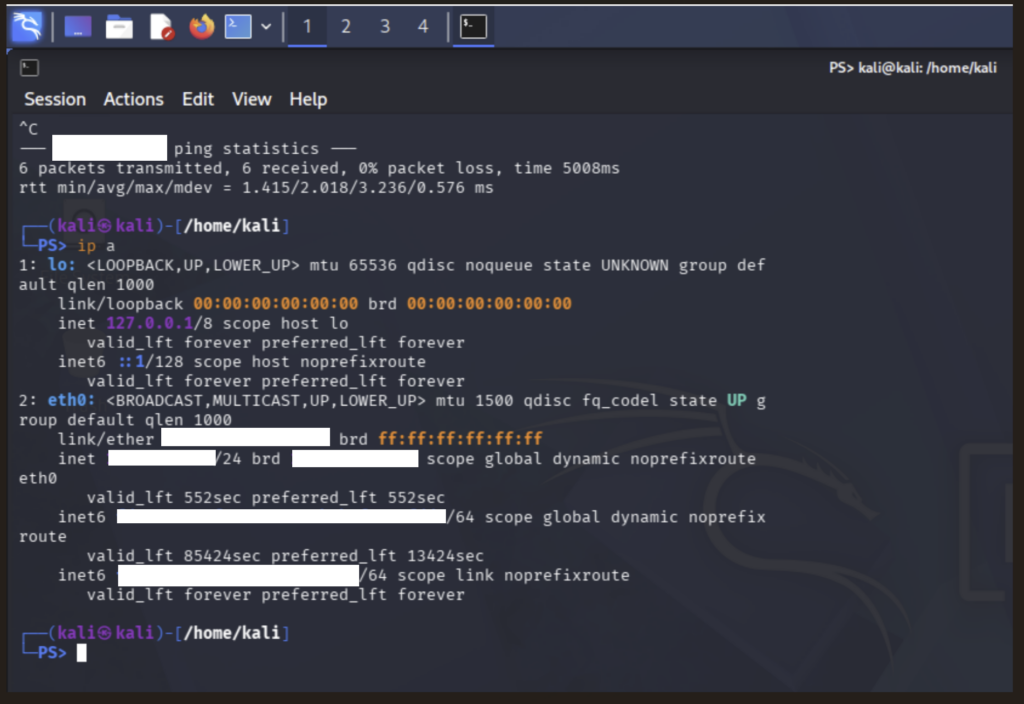
- Build a target machine and attacker machine.
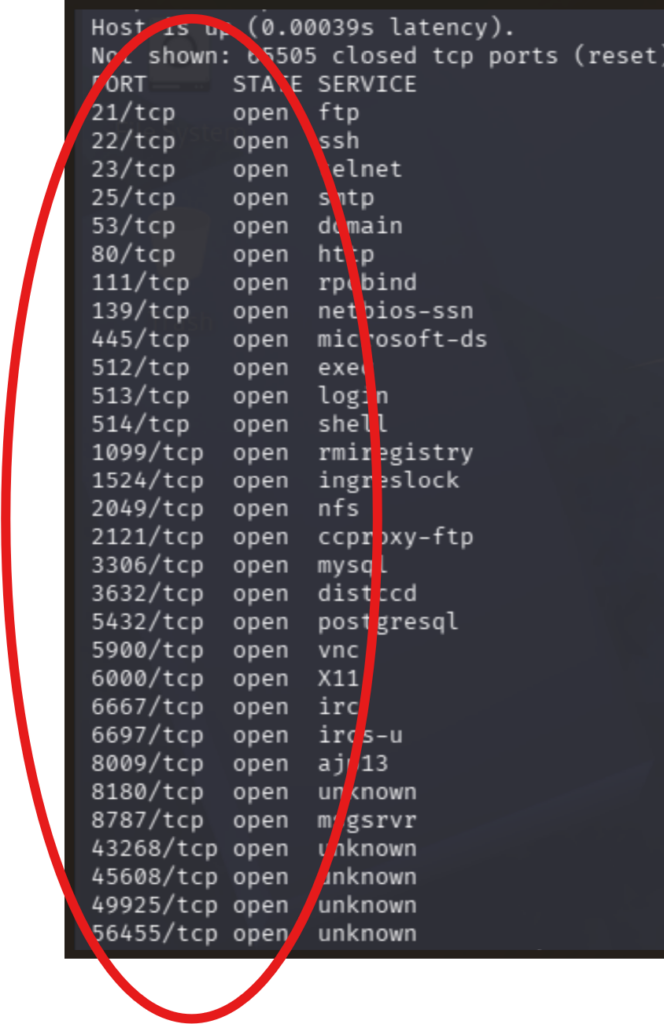
Use nmap command to:
>> Identify the ip of the all the hosts
>> Identify MAC address of all the hosts
>> Identify open ports and services running
>> Who is alive?
>> Port scanning
>> Service and Version detection
>> Aggressive scan
>> NSE Scripts
>> UDP Scanning
>> Stealth / Evasion Techniques
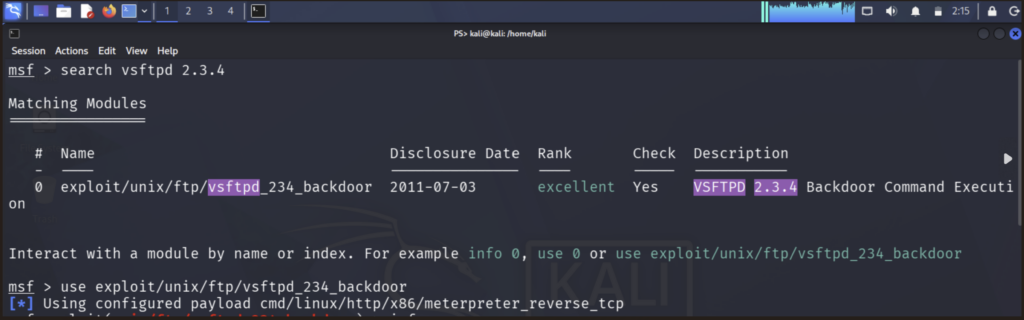
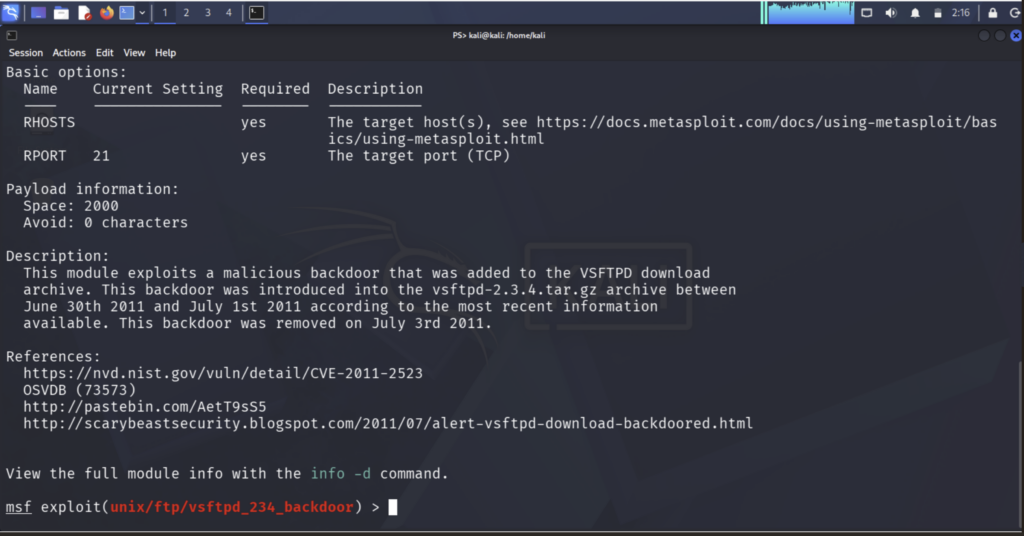
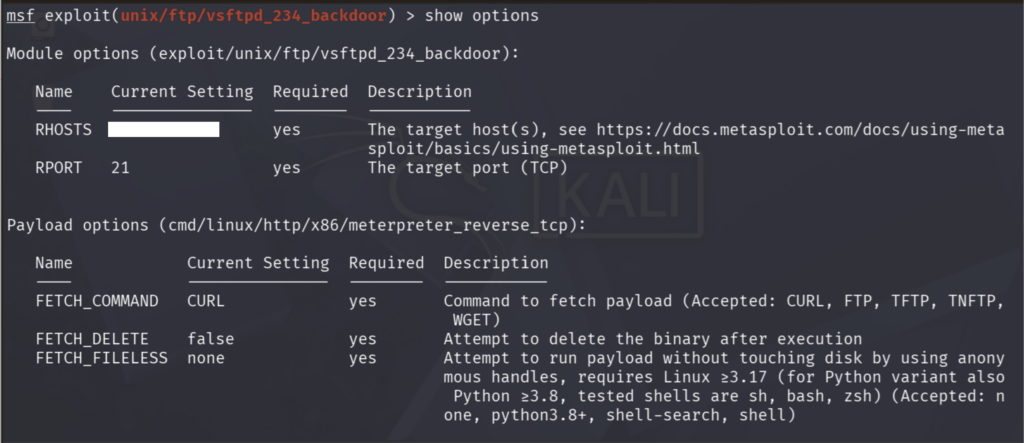
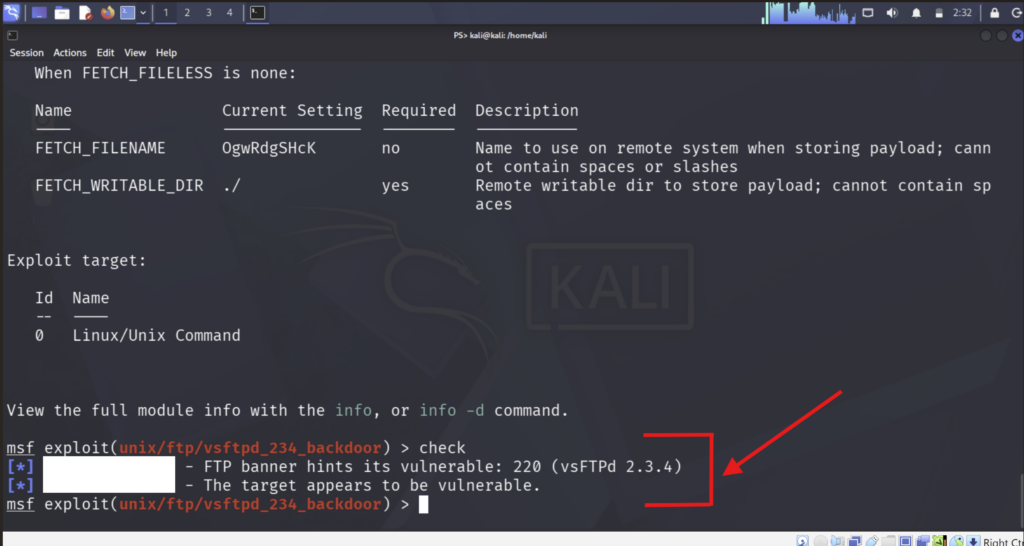
II. Exploitation with Metasploit

Practicing a standard ethical hacking process:
- Reconnaissance
Identify what’s running on the target (ports, services, versions) - Scanning
Use tools like Nmap to map services - Vulnerability identification
Look for known weaknesses (e.g., outdated services) - Exploitation (in lab only)
Use Metasploit modules that match the vulnerability - Post-exploitation
Understand what access means (privileges, persistence, etc.)
Practice scenario to be tested ethically ONLY in home practice lab:
- Hack the Box (Connection to remote service)
- Meow (Anonymous FTP access)
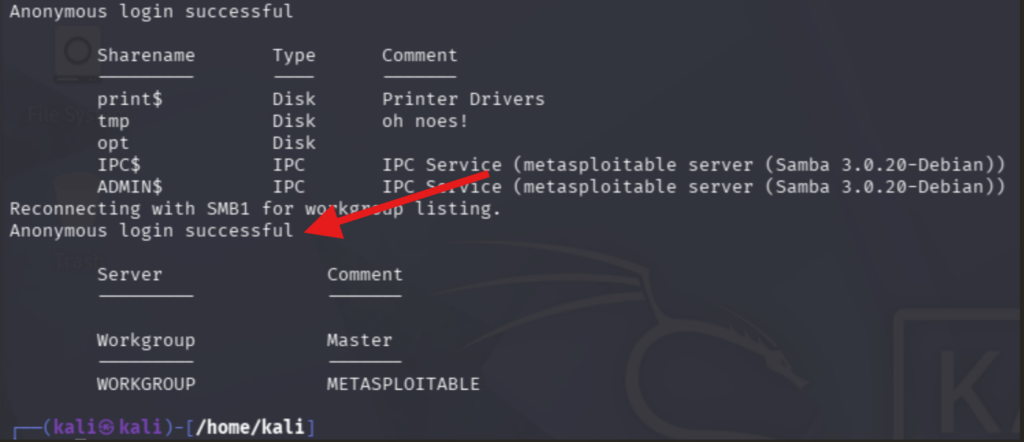
- Dance (SMB enumeration and file access) | smbclient -L //<target-ip>/ -N
- Vsftpd; DVWA; UnrealIRCd; Tomcat –> Misconfig scenarios
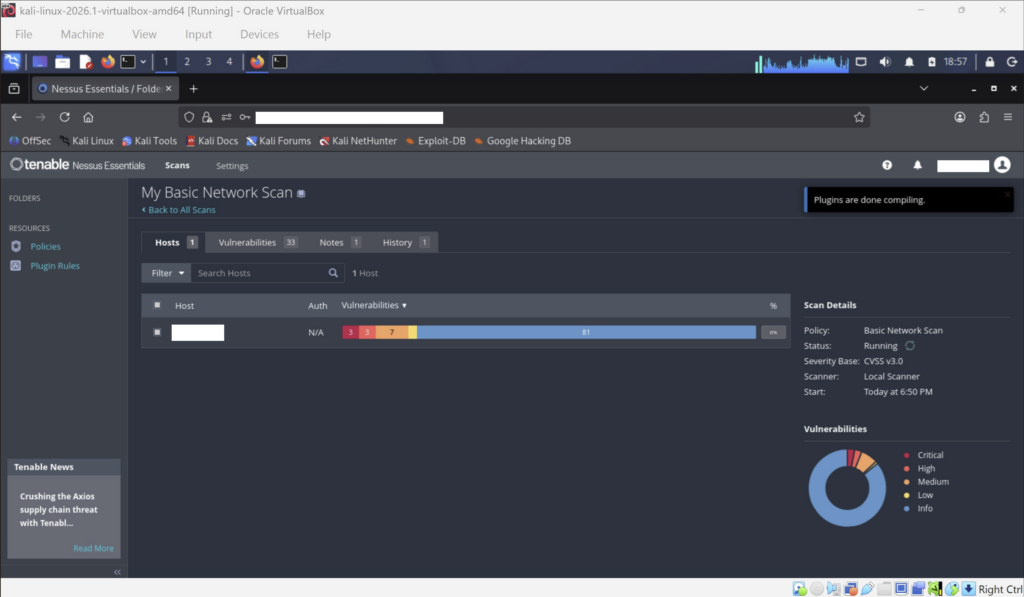
Identifying Vulnerabilities from Nessus
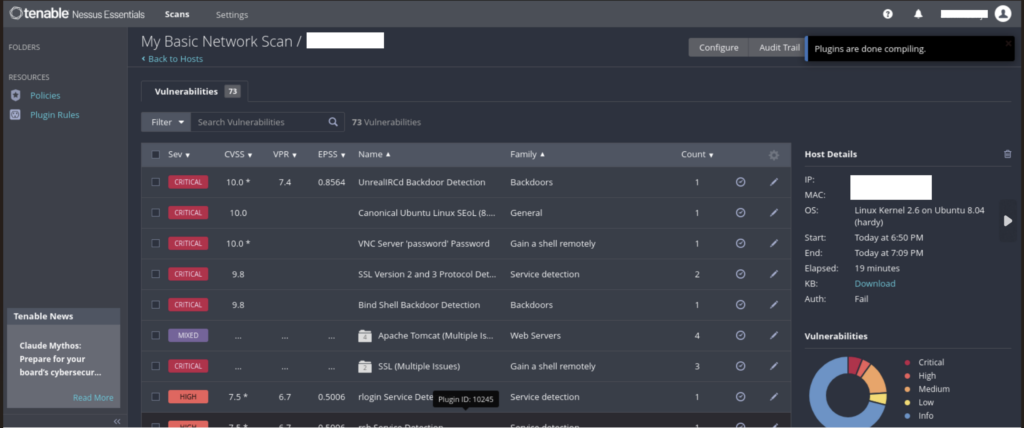
Things that could be learnt:
- Port scanning
- Identifying services
- Weak authentication
- FTP basics
- Anonymous login vulnerability
- File transfer
- SMB enumeration
- Shared folders
- Access without credentials
Identifying Vulnerabilities from Kali terminal
III. Log monitoring and analysis

What is happening across my system? How to detect suspicious activity? Where to start investigating an incident? Where and how to start responding to major security breaches? And this is where the importance of log monitoring comes into play. Honestly, configuring, analysing, and scavenging through heaps of log data could be very overwhelming and yes – boring!….But trust me, detective work becomes very enjoyable once you know what your objective is and what you are trying to look for.
Practice scenarios:
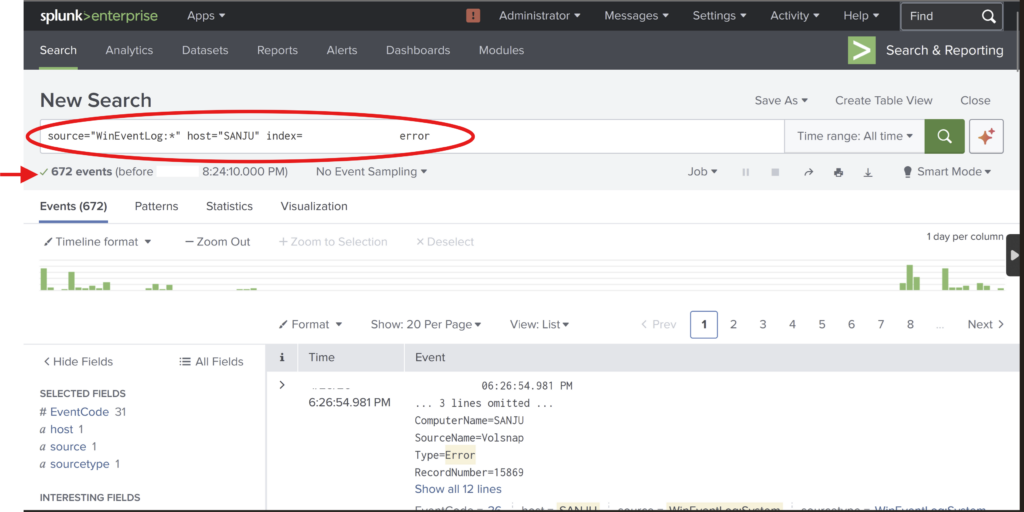
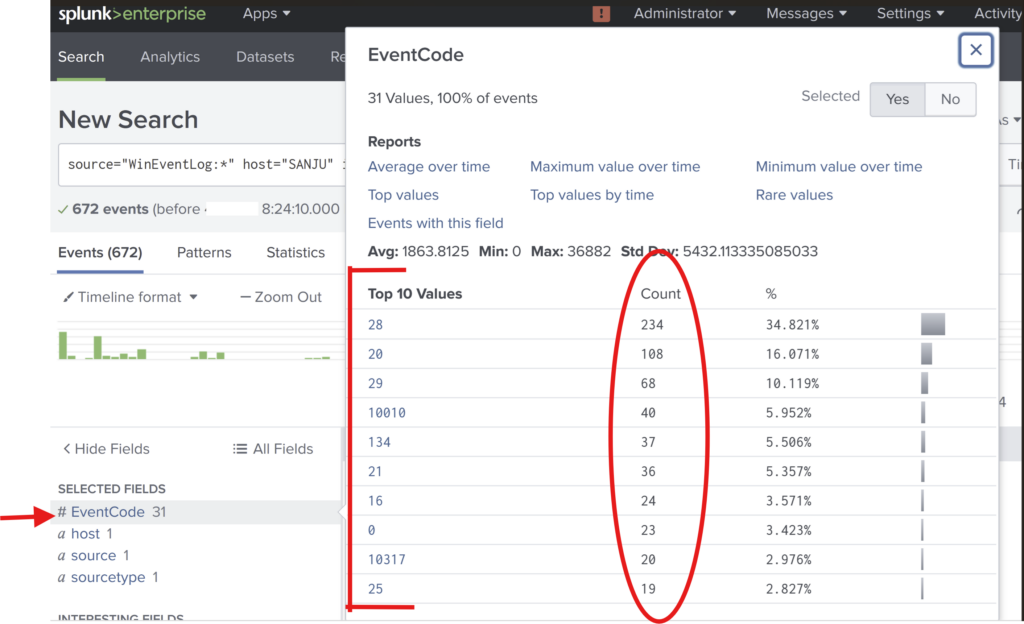
- Configuring log monitoring tools (here Splunk) in lab environment.
- Ingest data source to capture log information.
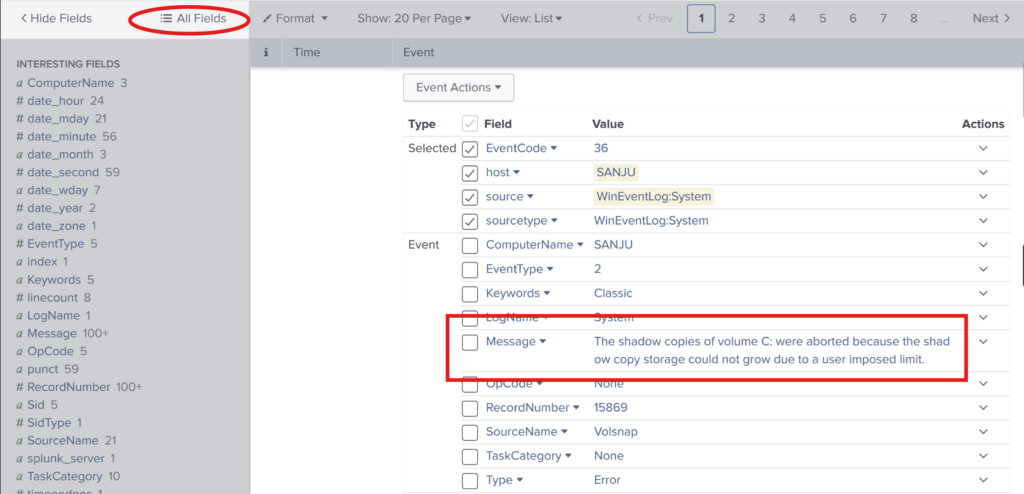
- Focus on important channels to look out for (if for a very basic example as host events then looking out for Security logs, Application logs, System logs etc.)
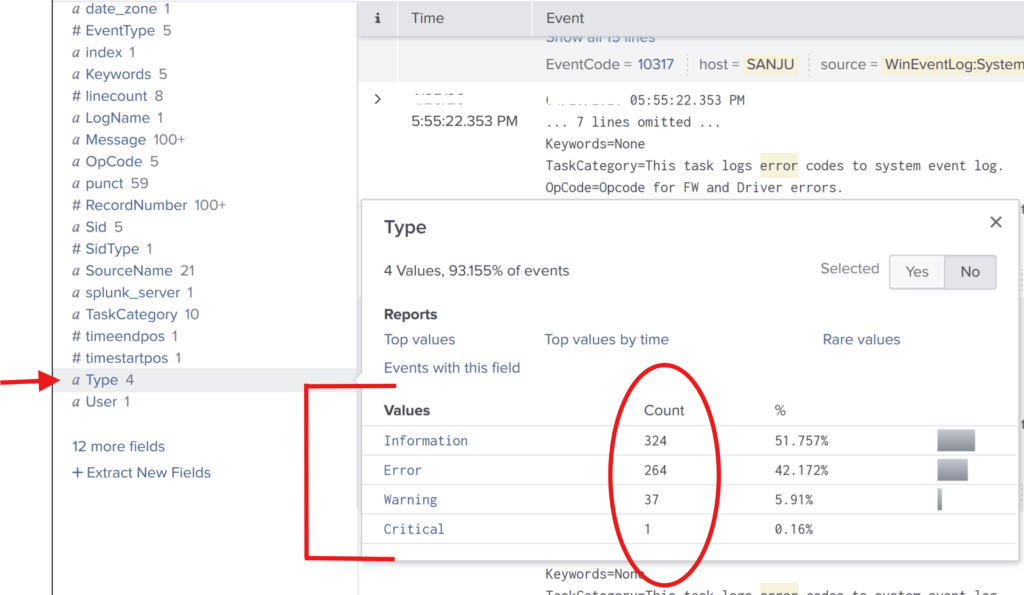
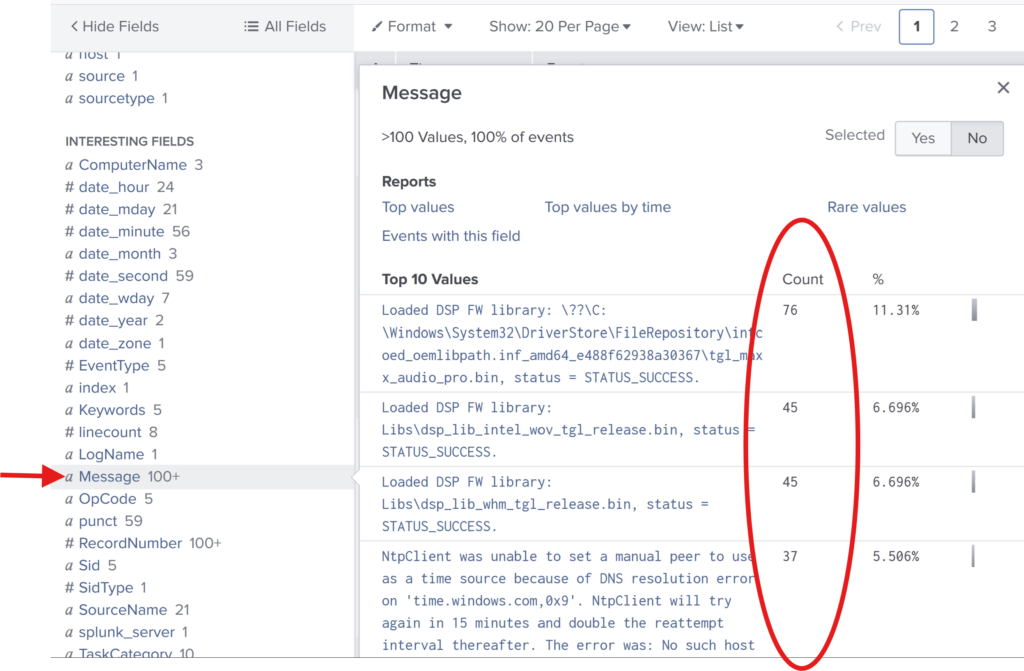
- Identify suspicious activity/patterns/error code/ event code.
- Analyze the logs with the error messages.
- Data in the form of report & visual representation.